DeFi Lending Protocol Security Risk Calculator
Security Risk Assessment
Based on Georgia Tech's 2025 research, this calculator estimates your security risk when using a DeFi lending protocol. Risk factors include protocol security measures and your personal safety practices.
When you lend crypto on a DeFi platform, you’re not handing money to a bank. You’re sending it into a piece of code - a smart contract - that’s supposed to act like a digital bank teller. It locks your assets, pays you interest, and lets others borrow against them. Sounds simple. But in 2025, lending protocol security remains one of the biggest open wounds in DeFi. Over $735 million was stolen from lending platforms in 2023 alone. And despite audits, insurance, and fancy marketing, users are still losing life savings to bugs no one saw coming.
How Lending Protocols Work (And Why They’re Dangerous)
Lending protocols like Aave, Compound, and MakerDAO let you deposit crypto and earn interest, or use your crypto as collateral to borrow other assets. No paperwork. No credit check. Just a wallet and a blockchain. That’s the appeal. But this freedom comes at a cost: total reliance on code. These platforms run on Ethereum and other Layer 1 blockchains. Every action - deposit, borrow, liquidate - is automated. If a smart contract has a flaw, it doesn’t get a second chance. It executes exactly as written, even if that means stealing your money. Unlike traditional finance, there’s no customer service line to call when things go wrong. No FDIC insurance. No freeze button. Once a hack happens, the funds are gone. And because blockchain transactions are public and irreversible, recovering stolen assets is nearly impossible.The Top 4 Security Risks in Lending Protocols
1. Flash Loan Attacks: The Invisible Heist
A flash loan lets you borrow millions of dollars - with zero collateral - as long as you pay it back within the same blockchain transaction. Sounds impossible? That’s the point. Attackers use flash loans to manipulate prices. Here’s how: they borrow $10 million in DAI, use it to artificially inflate the price of a token on a decentralized exchange, then borrow against that inflated price on a lending protocol. They withdraw more than they should, sell the tokens, repay the flash loan, and pocket the difference. All in under 15 seconds. The 2020 MakerDAO "Black Thursday" incident started with a crypto market crash. Price oracles didn’t update fast enough. Liquidations triggered in a chain reaction. Over $8 million in ETH was sold at pennies on the dollar. The protocol lost money because the code didn’t account for extreme volatility.2. Oracle Manipulation: Lying to the Code
Lending protocols need to know the real price of your collateral. If your ETH is worth $3,000, you can borrow up to $1,500 (at a 50% loan-to-value ratio). But if the oracle says ETH is worth $5,000, you can borrow $2,500 - even if it’s not true. Many protocols still rely on single-source oracles - like one API from a centralized exchange. That’s a single point of failure. Attackers can buy a small amount of a token on a low-volume exchange and spike its price. The oracle reports the fake price. The protocol lets users borrow more. Then the price crashes. The protocol is underwater. Users get liquidated. Attackers profit. The Inverse Finance hack in June 2022 was caused by a manipulated price feed. Attackers drained $15.6 million. The protocol used a TWAP (time-weighted average price) oracle, but the lookback window was too short. A quick pump-and-dump was enough to fool it.3. Reentrancy with Hookable Tokens
Most tokens on Ethereum follow the ERC-20 standard. But some malicious tokens are designed to "hook" into other contracts during transfers. When you deposit one of these tokens into a lending protocol, the token’s code runs during the deposit transaction. It can call back into the protocol - again and again - to drain funds before the deposit even finishes. This is called reentrancy. It’s an old vulnerability, but still deadly. The September 2021 Compound exploit used this method. Attackers deposited a malicious token, triggered a reentrant call, and stole $58.7 million. The code wasn’t poorly written - it just didn’t account for tokens that could behave differently than expected.4. Interconnected Risk: The Domino Effect
DeFi isn’t a collection of isolated apps. It’s a house of cards. Aave lends to Compound. Compound uses Chainlink oracles. Chainlink feeds data to MakerDAO. If one protocol gets hacked, the damage spreads. In 2023, a vulnerability in a small lending protocol caused a ripple effect. Its tokens were used as collateral on three major platforms. When the hack happened, those tokens dropped in value. All three platforms triggered mass liquidations. Over $120 million in collateral was wiped out in hours. No single protocol was at fault. But the system as a whole collapsed.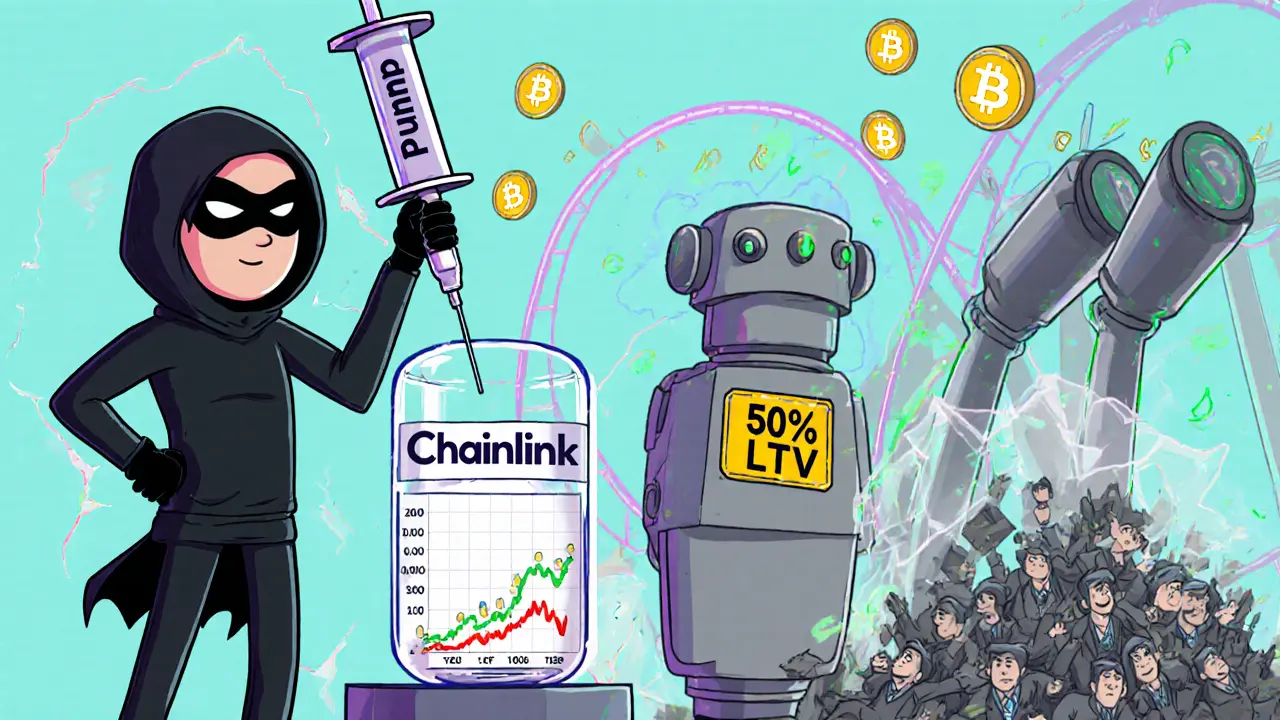
Why Audits Don’t Always Save You
Most protocols claim they’ve been "audited." That sounds reassuring. But audits aren’t magic. They’re snapshots. A firm like OpenZeppelin or Trail of Bits reviews the code once - before launch. If a new exploit is discovered months later, the audit doesn’t update. Georgia Tech’s 2025 study found that 69% of the protocols hacked in 2023 had already passed audits. Many ignored the auditors’ warnings. Others made changes after the audit and never rechecked. One protocol paid $120,000 for an audit, then added a new feature two weeks later. That feature had a reentrancy bug. The audit didn’t catch it. The hack cost $22 million. Even top protocols aren’t safe. Compound was audited. Aave was audited. MakerDAO was audited. All three were hacked. Audits reduce risk - but they don’t eliminate it.What’s Being Done to Fix This?
The industry is waking up. Here’s what’s working:- Decentralized oracles: Chainlink is used by 78% of the top 20 lending protocols. It pulls data from 35+ sources, not just one. That makes manipulation much harder.
- Formal verification: Some protocols now use math to prove their code works correctly. This isn’t testing. It’s proving. It takes longer and costs more - up to $200,000 - but it catches bugs no human reviewer can find.
- Dynamic liquidation thresholds: Aave adjusts how much you can borrow based on market conditions. If volatility spikes, the system automatically lowers your borrowing limit. That prevents flash loan exploits from working.
- Circuit breakers: Compound’s version 2.0, launched in April 2025, pauses liquidations if prices swing too fast. It gave the system breathing room during a 12% ETH drop in one hour - preventing $180 million in unnecessary liquidations.

What You Can Do as a User
You can’t fix the code. But you can protect yourself:- Don’t put in more than you can afford to lose. If you’re earning 8% APY on a new lending protocol, assume half your deposit could vanish.
- Check the oracle setup. If a protocol uses only one price source, avoid it. Look for Chainlink or other multi-source oracles.
- Watch the collateral ratio. Keep your loan-to-value below 60%. Higher ratios mean you’re one price drop away from liquidation.
- Use hardware wallets. 68% of users who lost money in 2023 used software wallets. Hardware wallets can’t be hacked remotely.
- Don’t trust audits alone. Look for protocols that have been live for over a year with no major exploits. New = risky.
The Bottom Line
Lending protocols are powerful. They’ve given millions of people access to financial tools that were once locked behind banks and brokers. But they’re also dangerous. The code is unbreakable - until someone breaks it. The good news? The industry is learning. Security practices are improving. The bad news? Attackers are learning faster. New exploits emerge every month. What worked last year won’t protect you today. If you’re using a lending protocol, assume it will be hacked. Plan for it. Limit your exposure. Understand the risks. And never, ever treat DeFi like a bank. It’s not. It’s a wild west - and the only sheriff is your own caution.Can lending protocols be hacked even after being audited?
Yes. Audits are snapshots in time. They review code once, before launch. If a protocol updates its code later - adding new features or changing parameters - those changes aren’t audited again. Many hacks in 2023 occurred in protocols that had passed audits but ignored follow-up warnings or made unreviewed changes. Audits reduce risk, but they don’t guarantee safety.
What’s the biggest cause of losses in DeFi lending?
Flash loan attacks and oracle manipulation are the top two causes. Flash loans let attackers borrow huge amounts without collateral to manipulate prices. Oracle manipulation tricks the protocol into thinking assets are worth more than they are, allowing users to borrow too much. These two vectors caused over 60% of the $735 million lost in DeFi hacks in 2023, according to Georgia Tech’s analysis.
Are decentralized oracles like Chainlink foolproof?
No. Chainlink is the most secure option available, pulling data from 35+ sources and using median values to avoid outliers. But even Chainlink has been manipulated in rare cases - usually when attackers target low-volume markets or exploit timing gaps in price updates. No oracle is 100% secure. The goal is to make attacks expensive and difficult. Chainlink does that better than single-source oracles.
Why can’t you recover funds after a DeFi hack?
Blockchain transactions are irreversible by design. Once a hacker transfers your crypto to a wallet they control, there’s no central authority to reverse it. Even if you know the hacker’s address, you can’t freeze or seize the funds. Law enforcement rarely recovers DeFi theft because wallets are anonymous and cross-border. Recovery is nearly impossible - which is why prevention is critical.
Should I use lending protocols at all?
You can, but only if you treat it like high-risk investing - not savings. Stick to well-established protocols like Aave or Compound with strong security track records. Use hardware wallets. Never stake more than you can afford to lose. Avoid new or low-TVL protocols. Understand how liquidations and oracles work. If you’re not comfortable with the risks, keep your crypto in a non-custodial wallet and avoid lending entirely.

