A Sybil attack is one of the most dangerous but often misunderstood threats to blockchain networks. At its core, it’s not about hacking a single wallet or stealing coins. It’s about lying to the network-by pretending to be hundreds or thousands of different users when you’re really just one person. And if it works, it can break the entire system.
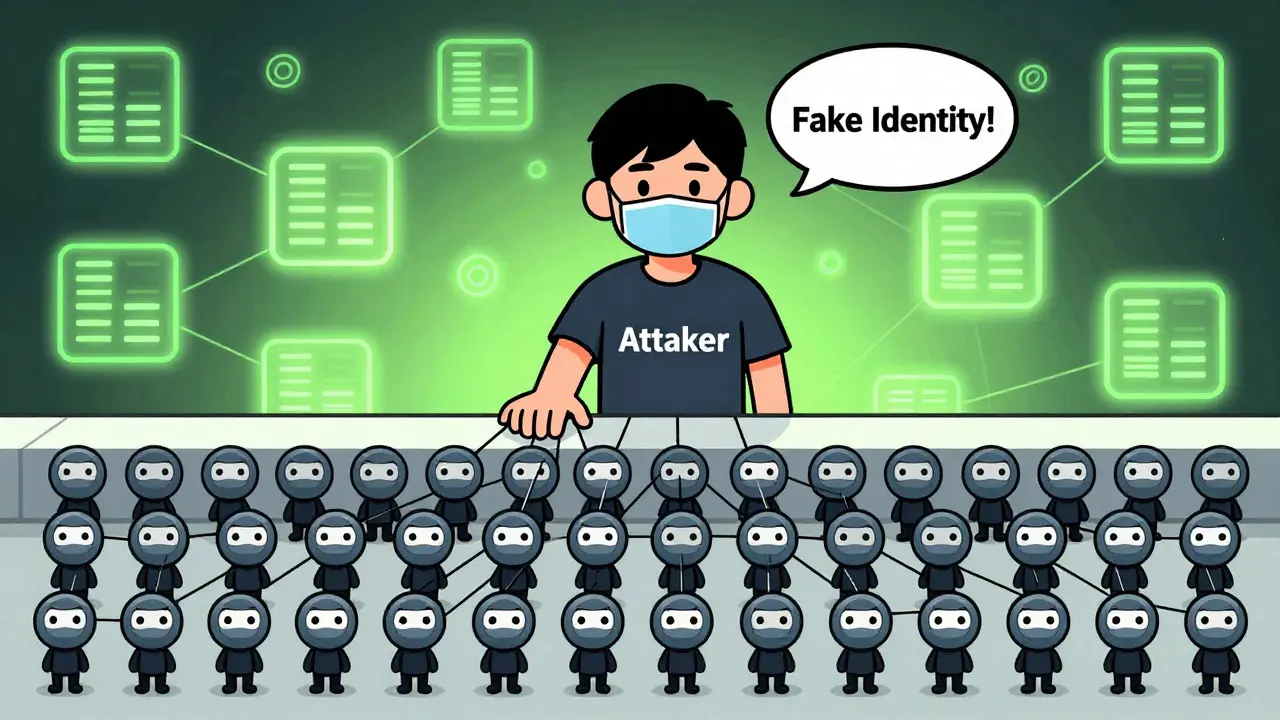
Imagine a voting system where anyone can show up and cast a vote. Normally, that’s fair. But what if one person shows up with 500 fake IDs, all claiming to be different voters? They can now control the outcome. That’s exactly what a Sybil attack does on a blockchain. The attacker creates dozens, sometimes hundreds, of fake nodes-each appearing as a unique participant-while all of them are controlled by a single entity. These fake nodes are called Sybil nodes.
Where Did the Name Come From?
The term "Sybil" comes from a 1973 book and movie about a woman with 16 distinct personalities, diagnosed with what’s now called Dissociative Identity Disorder. The researchers who first described this kind of attack in peer-to-peer networks-Brian Zill and John R. Douceur at Microsoft-used "Sybil" because it perfectly captured the idea of one person masquerading as many. In blockchain, that’s exactly what happens: one attacker becomes hundreds of fake participants.
How a Sybil Attack Actually Works
Blockchain networks rely on consensus. That means every node-the computers connected to the network-must agree on what transactions are valid. In Bitcoin, for example, miners compete to solve math problems and add new blocks. In Ethereum, validators stake cryptocurrency to propose and vote on blocks. But if you can flood the network with fake nodes, you can tilt the balance.
Here’s how it plays out:
- An attacker sets up dozens or hundreds of nodes using cheap cloud servers or automated scripts.
- Each node joins the network and appears as a legitimate peer.
- Because the network doesn’t know these are fake, it treats them like real users.
- The attacker then uses these fake nodes to manipulate voting, isolate other nodes, or block valid transactions.
For example, in a Proof-of-Stake network like Ethereum, each validator gets voting power based on how much ETH they stake. But if an attacker can create 100 fake validators-even with tiny amounts of ETH-they can still influence the consensus process if the system doesn’t properly limit identity creation. In Proof-of-Work systems, the attacker doesn’t need coins-they just need computing power. But since each node is a separate identity, even low-power machines can be used to create fake participants.

The Real Damage: More Than Just Fake Votes
A Sybil attack doesn’t just mess with votes. It can trigger a chain reaction of other attacks:
- Network Fragmentation: The attacker isolates certain nodes from the rest of the network. Those nodes start receiving false information and think the blockchain looks different than it actually does. This leads to confusion and broken consensus.
- Eclipse Attacks: This is a more targeted version. The attacker surrounds a single node with dozens of Sybil nodes, cutting it off from real peers. Then, they feed it fake transactions. The node thinks it’s seeing the real blockchain-but it’s all lies.
- 51% Attack Precursor: The biggest fear? Sybil attacks are often the first step toward a 51% attack. If you control enough fake nodes, you can eventually gain control of more than half the network’s resources-whether it’s hash power or staked coins. Once you have that, you can reverse transactions, stop others from sending money, or double-spend coins.
Double-spending is the nightmare scenario. You send 10 ETH to a merchant, wait for it to confirm, then use your Sybil nodes to rewrite the blockchain and erase that transaction. Suddenly, you’ve got your ETH back-and the merchant got nothing.
How Blockchains Fight Back
Blockchains aren’t defenseless. Over the past decade, developers have built multiple layers of protection:
Proof of Work (PoW)
PoW, used by Bitcoin, makes Sybil attacks expensive. You can’t just spin up a fake node-you need real computing power to mine blocks. Each node you control must solve complex math problems. The more nodes you create, the more electricity, hardware, and money you burn. It’s not impossible, but it’s wildly impractical. A Sybil attack on Bitcoin would cost millions in electricity alone.
Proof of Stake (PoS)
PoS, used by Ethereum, Cardano, and others, adds an economic barrier. To become a validator, you must lock up real cryptocurrency. If you try to create 100 fake validators, you need 100 times the staked coins. That means real money at risk. If you behave badly, you lose it all. This turns Sybil attacks into a financial suicide mission.
Node Reputation Systems
Some networks track node behavior over time. Nodes that consistently relay valid data gain trust. Nodes that send bad information or disappear too often get flagged or banned. This makes it harder for new fake nodes to blend in.
Identity Bound to Ownership
Some newer blockchains, like those using Atomic Ownership models, avoid the node-voting system entirely. Instead of trusting nodes, they trust cryptographic signatures. If you own an asset, you sign transactions with your private key. No voting. No fake nodes. No Sybil attack possible. The system doesn’t care how many participants there are-it only cares if the signature is valid.

Why This Still Matters Today
Large blockchains like Bitcoin and Ethereum are nearly immune to Sybil attacks because of their size and economic cost. But smaller chains? They’re vulnerable. Many new DeFi protocols, layer-2 networks, and private blockchains don’t have the same resources or security budgets. They often cut corners-using lightweight consensus or skipping node verification-and that’s where attackers strike.
In 2024, a research team from the University of Cambridge found that 12% of smaller blockchain networks had measurable Sybil activity. Some had over 40% of their "validators" controlled by just three entities. These aren’t theoretical risks-they’re happening right now.
Even social blockchains-chains built for decentralized social media-are at risk. If an attacker can create fake accounts to push a narrative, they can manipulate votes on content moderation, token distribution, or governance decisions.
What You Can Do
If you’re just a user, your main defense is simple: use well-established networks. Bitcoin, Ethereum, and other top-tier chains have proven defenses. Avoid small, obscure blockchains unless you know how they handle identity.
If you’re building a blockchain or running a node:
- Use Proof of Stake with slashing conditions.
- Implement node reputation scoring.
- Limit how many identities one IP or device can create.
- Monitor for sudden spikes in new nodes joining the network.
There’s no silver bullet. But combining economic cost, reputation tracking, and cryptographic verification makes Sybil attacks too expensive and too risky to be worth it.
Can a Sybil attack steal my crypto directly?
No, a Sybil attack doesn’t hack your wallet or guess your private key. It doesn’t steal funds directly. Instead, it manipulates the network to make false transactions look valid. If the attacker gains control, they might reverse transactions or double-spend coins-but only if they can convince the network to accept the lie. Your crypto is safe as long as the network stays honest.
Is Bitcoin vulnerable to Sybil attacks?
Bitcoin is extremely resistant to Sybil attacks because of Proof of Work. To create a fake node, you need real mining hardware and electricity. Even if you controlled 1,000 fake nodes, you’d still need more hash power than the rest of the network combined to change anything. The cost is astronomical-hundreds of millions of dollars-making it practically impossible.
Can a Sybil attack shut down a blockchain?
It can’t shut it down entirely, but it can cripple it. By fragmenting the network or isolating key nodes, attackers can cause delays, reorganizations, and confusion. Users may stop trusting the network if transactions aren’t confirming properly. In extreme cases, this leads to a loss of confidence and a drop in value or adoption.
Do all blockchains use the same defenses against Sybil attacks?
No. Bitcoin uses Proof of Work. Ethereum uses Proof of Stake. Some private blockchains use centralized permission lists. Others use reputation systems or identity binding. The best defenses combine economic cost (like staking) with technical barriers (like node reputation). Smaller chains often lack these layers, making them far more vulnerable.
Has a Sybil attack ever succeeded on a major blockchain?
Not on Bitcoin or Ethereum. But there have been confirmed cases on smaller networks. In 2023, a DeFi chain called ChainX suffered a Sybil attack where 78% of validators were controlled by a single entity. The network was temporarily halted, funds were frozen, and the community had to fork the chain to recover. This shows that while big chains are safe, the rest are still at risk.

This is actually one of the clearest explanations I've read. I used to think Sybil attacks were just about spam bots, but the idea of fake nodes manipulating consensus? That's terrifying. Especially how they can isolate nodes and feed them lies. We need way more awareness about this.
so like... if i make 500 fake wallets on my laptop, i can just vote myself into being the pope of crypto? lol
this is wild but also kinda obvious if you think about it 😅 blockchain is just a bunch of computers agreeing on stuff... what if one guy owns all the agreeing?
The philosophical weight here is staggering. A Sybil attack isn't just a technical flaw-it's a metaphysical betrayal of trust. We built these systems on the idea that identity is distributed, decentralized... but what if identity itself can be faked? It mirrors our social collapse: influencers with fake followers, bots masquerading as humans. The blockchain just made it visible.
PoW is just a band-aid. They say Bitcoin's secure? Nah. It's just that the cost to attack is so high no one's bothered. But if a nation-state wanted to? They'd do it in 48 hours. The real vulnerability isn't the tech-it's the assumption that people won't pay $500M to break it.
Let’s be brutally honest: most "decentralized" blockchains are centralized in practice. The so-called validators? Often controlled by VC-backed entities with 50+ nodes each. The "Sybil attack" isn’t some external threat-it’s the default state of 90% of chains. We’ve been gaslighting ourselves into believing in decentralization while the real power sits in a few AWS instances in Virginia.
I’ve been saying this for years: the entire crypto ecosystem is a honeypot for state actors. Sybil attacks? Please. The real threat is when governments quietly run thousands of validator nodes under shell companies and quietly rewrite history. No one talks about this because the narrative is "decentralization forever." But the truth? The blockchain is just another server farm with a fancy name.
USA built the internet. USA built blockchain. And now we're letting these tiny foreign chains with no security standards get away with murder? Wake up. If you're not running on Bitcoin or Ethereum, you're playing Russian roulette with your money. And don't even get me started on those "social blockchains"-they're just TikTok with crypto.
I appreciate how the article ends with practical advice. But what struck me most was the quiet elegance of "atomic ownership"-where identity isn't tied to nodes at all. It’s like realizing the problem wasn’t the crowd... it was the voting system. If every transaction is signed by the owner, you don’t need to count votes. You just need to verify signatures. Simple. Elegant. Unhackable. Why isn’t this the default?
I live in a country where people think blockchain is just for money... but this explains why it matters for democracy too. Imagine if your town voted on local laws and someone showed up with 300 fake IDs. That's what's happening in DAOs right now. We need to treat identity like a sacred thing-not a free-for-all.
You guys are overcomplicating this. If you want to stop Sybil attacks, just require a phone number. Or a passport scan. Or a one-time fee. The whole "decentralized utopia" is a fantasy. Humans are lazy. They want convenience. If you make it easy to join, you make it easy to game. Simple.
I’ve been running a node for three years and I’ve seen this play out firsthand. Early on, we had 200 new nodes join in a single day-all from the same IP range. We flagged them, analyzed their behavior, and found they were all relaying identical, malformed data. We implemented reputation scoring and cut them off. The network stabilized within hours. It’s not magic-it’s just good hygiene. Monitor. Log. Score. Ban. Repeat. Anyone can do this if they care enough.
I love how this post connects Sybil attacks to social media manipulation. It’s the same playbook: fake accounts, coordinated influence, algorithmic amplification. The blockchain just made it transparent. We’re not fighting hackers-we’re fighting human nature. The solution isn’t just technical. It’s cultural. We have to stop treating anonymity as a virtue and start demanding accountability.
I’ve been in crypto since 2017. I’ve seen 3 chains die from Sybil attacks. One was a "decentralized Reddit" where a single user created 1,200 accounts to vote themselves into governance. They then slashed the treasury and ran off with $8M. The community never recovered. This isn’t theory. It’s history. And it’s repeating.
I just want to say... this is the most important thing I’ve read all year. I’m not even in crypto. But if we can’t secure identity in digital systems... what hope do we have for democracy? For truth? For anything? I’m scared. And I think we all should be.
ok so if i get a sybil attack on my pet coin... can i just say "oops" and fork it? 🤷♀️
The notion that a blockchain can be secure without identity verification is a metaphysical delusion. The foundation of all social order-whether tribal, civic, or digital-is the recognition of bounded, accountable agency. To deny this is to invite chaos. Proof-of-Stake, while elegant, still permits infinite identity proliferation under the guise of decentralization. True security requires ontological constraint: one identity, one stake, one voice. Anything less is not a system-it is a theater.
I'm just glad someone finally explained this without jargon. So if I'm using a small chain, I should just assume it's compromised? 😅
The author’s conclusion is dangerously naive. "Use well-established networks" is not a solution-it’s a surrender. What happens when Ethereum becomes the target? What happens when a nation-state decides to weaponize Sybil nodes against the entire PoS ecosystem? The answer is not to avoid small chains-it’s to demand universal, auditable identity constraints across all protocols. Otherwise, we’re all just waiting for the next collapse.